Project background
Connected-vehicle features — remote lock, start, climate, diagnostics — require careful security beyond consumer-grade practices. The client needed a control path they could confidently offer to customers.
Challenge
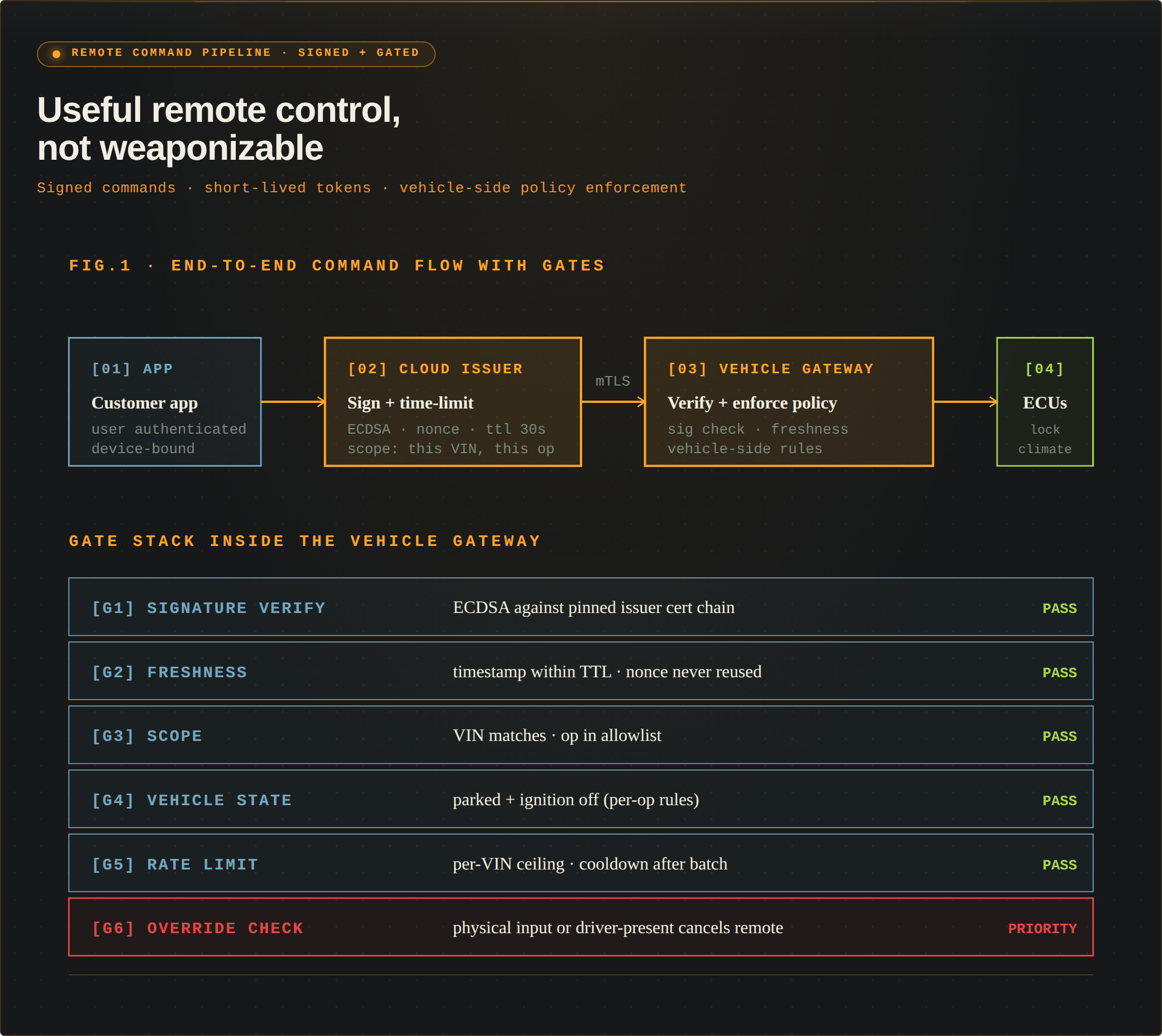
Designing remote actions that are useful yet cannot be weaponized, handling key management at vehicle scale, and making the system auditable end-to-end.
Approach & solution
We built a command pipeline with signed commands, short-lived tokens, and a vehicle-side gateway that enforces policy regardless of message source. Every action is logged and traceable, and the physical vehicle always retains override authority.
Results & benefits
The control path passed security review and shipped into the client's connected-vehicle offering. Customer-reported incidents have stayed in the benign-misuse category, with no compromise-class events.